This article was originally written for Windows Vista. These steps have not been tested under Windows 7, but they should work the same. The author will re-visit this article shortly.
If you are looking for
"the update server is not responding, which means it might be offline at the moment, or the Internet or Firewall settings may be incorrect."
--this is a classic indication of a Firewall (Microsoft's or your Virus Scanner suite) blocking the traffic. See details, below. If you are not using a software firewall, this article may not help solve this problem.
Contents:
* Do you have a firewall installed?
* Blocking Outbound Traffic with "wf.msc"
* Configuring Base (normal) exceptions
* Operating System Exceptions (SVChosts/Windows Update)
* Network Printing Exceptions
* Acrobat Reader (and other) Update Exceptions
* Ping and TraceRT exceptions
* How to temporarily disable outbound Firewall Rules
All computers need Virus/Spyware scanners and a firewall -- but the firewall is the area most of us are weakest. This article attempts to explain how to manage the firewall in Microsoft Vista.
Firewall 101
Thanks to our Cable or DSL Modems, most of us are behind a hardware firewall. This type of firewall blocks inbound traffic by hiding the computer's real IP Address behind the router's address. The process is called "Network Address Translation (NAT)". "NATting" hides your computer's real address from the Internet and this blocks all unsolicited inbound connections.
Without this, a computer would be infected within seconds of being connected on the Net -- with no action required on your part; you don't even have to launch a browser. Laptops are at a particular disadvantage because they can leave their own network and possibly attach to a public router where NATing might be turned off. If this happened, the laptops were sitting ducks.
But none of this helps when your computer
already has spyware that sneaks out and sends data outbound;
a normal hardware firewall will do nothing
to stop this type of traffic.
already has spyware that sneaks out and sends data outbound;
a normal hardware firewall will do nothing
to stop this type of traffic.
Microsoft realized this, and starting with Windows XP SP2, a default software-firewall was installed and it monitored inbound traffic, solving the missing NAT problem.
Then, starting with Vista, the firewall's capabilities were expanded so it could watch outbound traffic. However, because this feature required more end-user skill and knowledge, this feature was turned off. In this article, I suggest enabling outbound blocking -- but be prepared for a little work.
Half-Height Firewalls: The Need
A firewall that blocks inbound traffic (for laptops or desktops) is a minimum standard, but if you are a more sophisticated end-user, you can do better.
Consider the following: Imagine you had accidentally installed a virus, and didn't know it. Perhaps it arrived in an email or your children passed over a website that offered a free music-download. Now imagine the virus was too new to be detected by your scanners. Keystrokes could be captured, websites redirected, data uploaded; all without your knowledge.
A hardware or simple default software firewall is not going to capture the stuff happening behind your back. A properly-configured software firewall can intercept outbound traffic even when virus scanners fail.
Do you have a Firewall Installed?
If you are using their suites, other vendors, such as ZoneAlarm, McAfee, Symantec and others, probably installed a firewall. If so, those programs have different procedures to follow, but if you did not, you are probably using the default Windows firewall. To see which firewall is installed, do the following:
A. Click Start, Settings, "Control Panel"
B. Open "Security Center"
C. Click the down-arrows on Firewall. If it says Windows Firewall, then this article is for you.

Blocking Outbound Traffic
By default, Vista (and Windows 7) firewall only blocks unsolicited inbound traffic. Follow these steps to block unknown outbound traffic. This is a relatively advanced topic.
1. Launch the Windows Firewall Control Panel:
Start, Run, "wf.msc"
The control panel takes several seconds to load
2. On the (left) tree-side, highlight the top of the tree "Windows Firewall with Advanced Security".
On the Right side, click "Properties"
3. For each of the top-tabs [Domain Profile, Private, and Public Profile],
set "Outbound Connections" to "Block"
Do this three times, once for each tab.

Important: When you do this, all internet traffic will be blocked and web-browsers, email programs, software updates, etc., all quit working until they are granted an exclusion (next).
4. Click OK when done, returning to the main Windows Firewall control panel.
Configure Base Exceptions
Next, grant exceptions to your most commonly used programs. For example, on my machine, I allow the following:
Internet Explorer (browser)
FireFox (browser) + Firefox Updater
Outlook (email)
Thunderbird (email) + Thunderbird Updater
Windows Media Player
Itunes (or other music-players)
Your Virus Scanner
Base Operating System Exceptions (details below)
*Windows Update / Windows Defender / MSE
DOS Ping
DOS TraceRt
Network Printing
Except for these exceptions, all other programs will not see the Internet and will think the computer is "off the net." This also means they cannot ask for automatic updates. In my opinion, this is good: for application software, update when you want so you are not surprised; I typically manually download updates from the web and do not rely on automatic updates. If you would rather have them update automatically, add them to the list above. There are more details on this in a moment.
Also, be aware that Windows Defender (Spyware scanner) and Windows (auto) update will not see the network, and this is addressed separately in a few moments.
For each program in the list above, follow these steps:
5. In the Windows Firewall Control Panel, main screen, click "Outbound Rules" (on the left-window).

6. On the right-side, click "New Rule".
Select "Program" and click Next
Choose "This Program Path" and browse or type the executable's .exe name.
For example, Internet Explorer is found at "C:\Program Files\Internet Explorer\iexplore.exe" (do not use quotes even though there are spaces in the name).
Firefox might be installed at "C:\Program Files\Mozilla\Firefox\Firefox.exe".
Windows Media Player is at "C:\Program Files\Windows Media Player\wmplayer.exe"

Hint: To find a program's location, locate the program's icon, other-mouse-click and choose Properties. Copy and paste the "target" field, minus any parameters.
7. On the Next Screen:
Choose "Allow the connection"
Recommend choosing all three Domains [Domain, Private, Public]
8. When prompted, give it a "pretty name" such as "A-Internet Explorer" (I always like to prefix the programs I added by using an "A-" so they sort at the top of the list). As you can see, this screen is complicated and the A-dash helps organize it.

9. Add the other programs in the list, following the same steps.
If you forget to add a program, it simply won't connect to the Internet. For example, if you play a store-bought game that can connect to the Net, it will not work until granted an exception here.
The benefits are this: If a rogue program installs itself, the firewall blocks its ability to talk to the outside world and your computer will be safer. (Here it would be nice if the Windows Firewall would announce that program "XYZ is attempting to connect to the Internet" so you would know the virus was there. Perhaps this will be fixed in later versions.)
Operating System Exceptions
Windows Update and Windows Defender also need an exception. You *must* do these in order to adequately protect your system. If not, you will get this error: Windows could not search for new updates. Error(s) found: Code 80072EFD:

Follow these steps to grant an Exception in the Firewall.
1. As before, create a new Outbound Rule, selecting this program:
C:\Windows\System32\svchost.exe
Name the rule "A-Svchost" so it sorts with the others.
When selecting "svchost," Windows will display a warning. Ignore the warning and allow it to create the rule, but because this is an operating-system file, additional steps should be taken and these are detailed next.
2. Edit the new rule's properties by double-clicking the name ("A-svchost").
3. Illustrated below, select the [Programs and Services] tab
Click the "Settings" button.
4. Choose the radio-button "Apply to this service"
In the list, choose "Windows Update";
Click OK
5. In the "Protocols and Ports" tab
Change the Protocol Type from Any to "TCP"
Change the Remote Port from All Ports to "Specific Ports"; type ports "80, 443"

Save the changes and close the entire control panel. Windows Update and Windows Defender should now work properly.
Printing Exceptions
Microsoft was not thinking when they wrote the firewall software -- it surprisingly blocks IP-based Network printing. This turns out to be nuisance and you have to go to two different places to set the exception properly.
Follow these steps if you have a printer connected to a (Jet Direct or other IP-based print spoolers). If the printer is a USB or LPT printer attached to your local machine, you do not need to use these steps.
1. Start, Run, "FirewallControlPanel.exe" (or select Control Panel, Security Center, Windows Firewall).
2. Choose "Allow a program through Windows Firewall"
3. Click the [Exceptions] tab
Choose [x] File and Printer Sharing
Click OK, OK, etc. to close the control panel / Security Center screens.
Next, go to the Advanced Settings:
4. Start, Run, "wf.msc"
5. In Outbound Rules, click "New Rule"; Select "Custom", then "All Programs"
6. On the next screen,
Choose Protocol Type "TCP"
Local Port: "All Ports"
Remote Port: "All Ports"
Click Next
7. "Which local IP address does this rule match?" Choose "Any"
Which remote IP Address does this rule match?
Choose "These IP Addresses"
Add your (JetDirect's Print Server's IP Address) under "This IP Address or subnet"
This will not be your local PC's IP address. For example, my printer spooler is defined at 192.168.200.251. This step is only needed on those computers that talk directly to the print spooler/JetDirect. If other computers connect to your computer in order to share the printer, nothing needs to be done on the remote machine. Click Next to continue.

8. Choose "Allow the connection", then choose all three domains [Domain, Private, Public]
9. Name the rule, per my recommendations: "A-Printer 192.168.200.251"
Clearly, if the PC is on a corporate network, network printing may be problematic. Consider using an IPAddress Range. I welcome suggestions on how to improve this.
Adobe Acrobat Reader Update
If you wanted Adobe Acrobat (or other programs, such as WordPerfect, your photo-editor, etc.) to auto-update, they may fail with a message similar to "the update server is not responding, which means it might be offline at the moment, or the Internet or Firewall settings may be incorrect." This is a classic indication the Firewall is blocking the traffic.
This is by design. In the Outbound rules, *all* programs are blocked unless granted an exception and Adobe's product has no way of knowing a firewall was in the way.

Finding the Program:
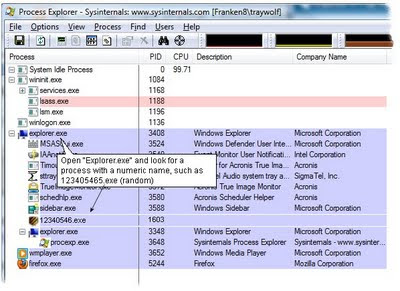
In this case, granting Acrobat Reader an exception (AcroRd32.exe) will not solve the problem because the Reader is not the program doing the updating. It takes a moment of sleuthing to find the real program; here are the steps.
A. Press ctrl-alt-delete, "Start Task Manager". Leave this window open.
B. Launch Acrobat Reader, select Help, "Check for Updates"
C. In Task Manager, note how a new program jumps into the list: "Adobe_Updater.exe". This is the program that needs a hole punched through the firewall.

D. In Task Manager, other-mouse-click the EXE name and choose "Open File Location". You will find it in "C:\Program Files\Common Files\Adobe\Updater6\adobe_updater.exe".
You may find that other update-programs do similar things. Of course, you could ignore the auto-updater and download the installation manually from the web. Since your web-browser has been granted permission, there will be no problems.
Other Recommended Files
A-Ping: %SystemRoot%\System32\PING.EXE
A-TraceRt: %SystemRoot%\System32\TRACERT.EXE
If you do not grant this exception, Ping will report a "General Failure"
Also, consider these, if you have these products installed:
C:\Program Files\Common Files\Adobe\Updater6\adobe_updater.exe
%ProgramFiles%\Mozilla\Firefox\updater.exe
%ProgramFiles%\Mozilla\Thunderbird\updater.exe
Temporarily Stopping Outbound Rules
Sometimes the firewall's outbound rules can get in the way with other software updates and it is more trouble than it is worth to grant an exception. For example, the Java client install has a new name with each new version and will report "The installer cannot proceed with the current Internet Connection settings."
To work around this, you would have to grant an exception (discussed above) for each new installation file; this is a drag because Java is updated frequently. It may be easier to temporarily disable outbound rules just for the install. Follow these steps:
1. Start, Run, wf.msc (the Windows Firewall Control Panel)
2. Highlight the top of the tree ("Windows Firewall with Advanced...")
3. Click "Windows Firewall Properties"
4. Click the [Private Profile] tab
Set Outbound Connections to "Allow"
5. Install the software, then return Outbound connections to "Block"
As an aside, when installing Java Runtime, I recommend unchecking the Yahoo Toolbar (it is spyware). Since an exception was not granted to either the installation routine or to the actual Java client, you might as well stop it from running its automatic updates (which is an endemic problem with Sun's Java).
Start, Run, MSConfig and uncheck Java's automatic update, as illustrated.
(click illustration for a larger view; click right-x to return)

Read more about startup programs here: Cleaning up Startup Programs
Maintenance
If you install a new version of a program, the firewall rules will still work, as long as the .exe name is the same (this is different than other vendors: their products recognize the change and ask confirmation when updates happen). At any time, you can go into the wf.msc control panel and disable a program's access to the internet by disabling the rule.
Conclusions
Configuring Windows Firewall for outbound traffic is a nuisance and the interface is not as friendly as I would like. For example, ZoneAlarm's free firewall, recommended for Windows XP but not for Vista, prompts on the fly when it detects a new program attempting to talk on the network. With one click, it can add an inclusion or exclusion and essentially self-configures.
In comparison, Microsoft's firewall is cumbersome and an average end-user could not make it work. The product is capable, but trudging through the wizards is a drag and the complicated main screen will scare most people away.
Related to this, when Microsoft's firewall blocks a program, it doesn't tell you the program was stopped. For non-computer-experts, this could be a good thing because they won't be bugged and they will never be able to grant an exception. On the other hand, if you are wondering why a program isn't working, it could be the firewall, but you may not remember to grant the exception.
Personally, I prefer ZoneAlarm's free Firewall and I use it on my Windows XP computers. But on Vista, ZoneAlarm has been troublesome and I've de-installed it, which forced me to use Microsoft's firewall.
Now that I know how to configure it, Microsoft's product is 'usable' and it is doing what it is supposed to do. I wished it had a report or some other way to notify that a program has made an outbound-attempt -- I definately see room for improvement here. I would like to hear your experiences with ZoneAlarm and Vista/W7.
In any case, whether you use these or other commercial products, it will take about a half-an-hour to configure a firewall. Once it is setup, it should require little maintenance.
Related content
Vista Spiffs
Disable Vista UAC Nags
Streamlining Windows Start Menus